Table of Contents
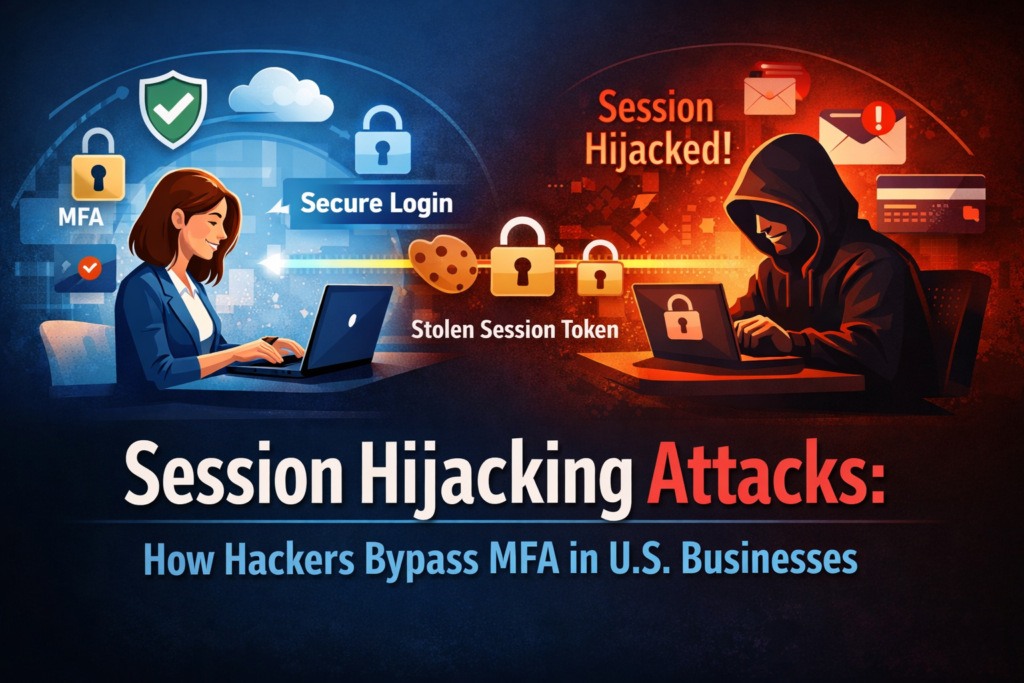
Session hijacking attacks are no longer just a technical cybersecurity term buried in enterprise threat reports. They are actively impacting U.S. small businesses, freelancers, and remote teams who believe Multi-Factor Authentication (MFA) alone keeps them safe.If you run a small business, manage client accounts, or work remotely from coffee shops and coworking spaces, this threat directly concerns you.Let’s break this down in simple, real-world terms.
What Are Session Hijacking Attacks?
Session hijacking attacks happen when a hacker steals or takes control of a valid, already-authenticated user session. Instead of cracking your password or bypassing MFA directly, attackers steal your active session token — the digital “proof” that you’ve already logged in successfully.Think of it like this:You show your ID (password) and security code (MFA) to enter a building.Once inside, you receive a visitor badge (session token).
A hacker doesn’t try to fake your ID.They steal your badge.And once they have it, they can walk around as if they are you.
Why Session Hijacking Attacks Are Growing in the U.S.
In the U.S., small businesses increasingly rely on:
- Cloud accounting tools
- CRM platforms
- Payroll systems
- Project management apps
- Remote access dashboards
According to the Federal Bureau of Investigation, business email compromise and account takeovers continue to cause billions in losses annually. Many of these attacks now involve session theft techniques rather than password guessing.Attackers target smaller organizations.because:
They assume MFA is enoughSecurity budgets are limitedEmployees use personal devices
How Hackers Bypass MFA Using Session Hijacking Attacks
Here’s the uncomfortable truth:
MFA protects the login process — not the session after login
1. Phishing With Reverse Proxy Tools
Attackers use phishing kits that clone legitimate login pages.
When you enter your password and MFA code, the attacker captures:
- Your credentials
- Your session cookie
Even though you completed MFA, they now have your authenticated session.The Cybersecurity and Infrastructure Security Agency has warned businesses about advanced phishing frameworks capable of bypassing MFA using session capture.
2. Malware That Steals Browser Cookies
If malware infects your device, it can extract:
- Session cookies
- Saved login tokens
- Active authentication sessions
Freelancers using unsecured public Wi-Fi or downloading pirated software are especially vulnerable.
Man-in-the-Middle Attacks on Public Networks
If you or your employees log into business dashboards on insecure networks, attackers may intercept session data.Even with HTTPS, poorly secured devices can leak tokens.
Real Risk for Small Businesses & Freelancers
Many U.S. small businesses assume:“We use MFA. We’re safe.”But session hijacking attacks allow hackers to:
- Access financial accounts
- Change payment instructions
- Download client data
- Send fraudulent emails
- Add new MFA devices
Worse, since the login appears legitimate, detection becomes difficult.The average small business often lacks 24/7 security monitoring, making these breaches more damaging.
Why Traditional MFA Isn’t Enough
Standard MFA (SMS codes, authenticator apps) verifies identity at login.But after authentication:
- The server issues a session token
- That token remains valid for hours or days
- Anyone holding it is trusted
This is the blind spot.Even major tech platforms have reported incidents where session tokens were stolen to bypass MFA protections.
Signs Your Business May Be Targeted
Watch for:
- Unexpected account logouts
- Login alerts from unknown locations
- MFA reset notifications you didn’t request
- Suspicious financial transfers
- Browser extensions behaving oddly
If something feels off, investigate immediately.
How U.S. Businesses Can Prevent Session Hijacking Attacks
Now the practical part.Here’s how small businesses and freelancers can reduce risk:
1. Use Phishing-Resistant MFA
Hardware security keys (FIDO2/WebAuthn) are far more resistant to session theft than SMS codes.They bind authentication to the legitimate domain, preventing proxy phishing attacks.
2. Enable Short Session Lifetimes
Reduce how long session tokens remain active. Shorter sessions mean smaller attack windows.
3. Use Secure, Managed Devices
Avoid logging into business dashboards from:
- Public computers
- Shared devices
- Outdated browsers
Keep systems updated.
4. Monitor Session Activity
Many cloud services provide:
- Active session tracking
- Device management dashboards
- Forced logout capabilities
Review them regularly.
5. Train Employees & Contractors
Awareness is critical.Train teams to:
- Verify URLs carefully
- Avoid suspicious login prompts
- Report unusual MFA behavior immediately
The National Institute of Standards and Technology also provides digital identity guidelines that businesses can reference for stronger authentication practices.
Why Freelancers Are Especially Vulnerable
Freelancers often:
- Use multiple client platforms
- Log in from various locations
- Reuse browsers across projects
- Install productivity extensions
Each of these increases session exposure risk.
One hijacked session could expose multiple client accounts — damaging reputation and trust.
The Financial Impact
Session hijacking attacks often lead to:
- Direct financial theft
- Data breach costs
- Legal liability
- Loss of client confidence
- Insurance premium increases
And for small businesses, recovery can be difficult.Unlike large enterprises, smaller organizations don’t always survive major cyber incidents.
The Future of Authentication in U.S. Businesses
Cybersecurity is shifting toward:
- Passwordless authentication
- Continuous session validation
- Device fingerprinting
- Behavioral analytics
MFA is no longer the final defense. It’s just one layer.Businesses must adopt layered security strategies to combat session hijacking attacks effectively.
Conclusion: Session Hijacking Attacks Are a Silent Threat
Session hijacking attacks are one of the most dangerous yet misunderstood cybersecurity threats facing U.S. small businesses and freelancers today.They don’t break in — they slip in quietly using trusted sessions.MFA alone is not enough.If you rely on cloud platforms, manage financial data, or operate remotely, now is the time to:
- Upgrade authentication methods
- Monitor sessions actively
- Educate your team
- Reduce session exposure windows
Cybersecurity isn’t just an IT issue — it’s a business survival strategy.If you want a practical checklist specifically designed for freelancers and U.S. small businesses, visit my blog for actionable cybersecurity protection guides and real-world prevention strategies.Stay secure. Stay informed.
Check out this blog:
AI Browser Extensions: Are They a Security Risk for U.S. Freelancers
