Table of Contents
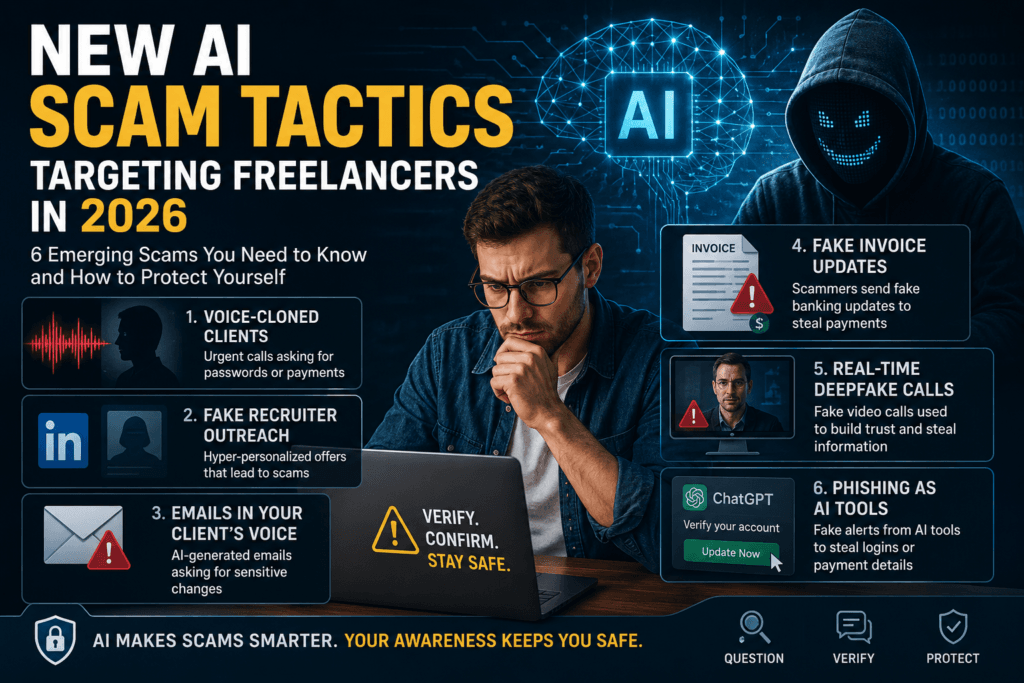
Freelance scams used to be obvious. Bad grammar, suspicious payment requests, a Gmail address pretending to be a Fortune 500 recruiter. The new wave is different. Most of it now uses AI. Voice clones of real clients. Fake recruiter pitches that have read your portfolio. Emails written in the tone of your last six months of correspondence.
Most of these patterns first appear at enterprise scale, where security operations teams see them daily before they trickle down to smaller targets.Many freelancers without dedicated IT support are especially vulnerable because they depend heavily on cloud tools, email communication, and remote workflows.The freelancer version is the same playbook in a different size.Six patterns showing up over the past 12 months, what they look like in practice, and one defense for each.
Voice-cloned clients calling about “urgent” account changes
Scammers scrape public audio of a freelancer’s actual client (podcast clips, YouTube interviews, conference recordings) and feed it into a voice model. Thirty seconds of clean audio is often enough to produce a passable clone. The scammer then calls the freelancer directly, sounding like the client, asking for a password reset, a payment to a new account, or admin access to a shared project.
Watch for: any phone call that references urgency, namechecks a real recent project, and asks you to bypass your usual workflow. Real clients almost never call out of nowhere with a payment change.
Defense: never act on a voice request alone. Confirm in writing through the channel you and your client already use. If they say it’s urgent, that’s the moment to slow down, not speed up.
Hyper-personalized fake recruiter outreach on LinkedIn
The new fake recruiter doesn’t send the same template to a thousand freelancers. AI tools read your last 50 LinkedIn posts, your bio, and your portfolio in seconds, then write outreach that sounds like a real hiring manager who’s done their homework. The scam ends in one of two places: a “paid test project” that never pays, or a request to set up an account on a payment platform that quietly drains your wallet.
Watch for: a job offer that arrives without a video call, references your work in unusual specificity, and pushes you toward an unfamiliar payment platform.
Defense: every legitimate client will agree to a short video call before sending money or signing a contract. If the recruiter resists, the offer is fake.
Emails written in your real client’s voice
If a scammer compromises one client account, or pulls enough public emails and LinkedIn messages, they can train an AI to write in that client’s exact tone. The phrasing matches. The signature matches. Even the typing quirks match. The email asks you to update banking details, click a shared file link, or send over a credential.
Watch for: any email asking you to change something operational. Banking,login, file location, account access.
Defense: lock your client’s bank details on first invoice and never change them based on an inbound message. If the request is real, your client will agree to verify it on a video call or through a co-signed document.
Manipulated invoices with fake “updated banking details”
This one targets the freelancer’s accounting workflow specifically. The scammer either intercepts a legitimate invoice you’ve sent or generates a fake “your client wants to switch accounts” notice with AI-faked email headers and matching design templates. The freelancer updates the bank details on file. The next payment goes somewhere else.
Watch for: any banking change request that arrives outside your normal contract or accounting flow.
Defense: lock your client’s bank details on first invoice and never change them based on an inbound message. If the request is real, your client will agree to verify it on a video call or through a co-signed document.
Real-time deepfake video calls
Real-time deepfake software has become accessible enough that a scammer can sit on a video call with a synthesized face and lip movement that holds up for 15 to 30 minutes. Used in fake interviews to build trust, ask probing questions about your client list, payment platforms, or login workflows. Sometimes followed by a “confidential test project” with a malware-laden file attachment.
Watch for: video that looks slightly off in good lighting, awkward pauses around natural background movement, and an interview that focuses more on your tools and accounts than your actual work.
Defense: ask for a brief unscripted moment on camera. Have them turn their head, pick up an object behind them, write a phrase on a piece of paper. Real-time deepfakes still struggle with sudden movement and natural depth.
Phishing dressed up as ChatGPT, Claude, Midjourney, and other AI tools
Freelancers are heavy users of AI subscription tools. Scammers know this and have built convincing “verify your account” or “your subscription is expiring” emails that lead to credential capture or stored payment theft. The emails pass the eye-test because the branding matches and the AI-generated copy is clean.
Watch for: any email about an AI tool subscription that includes a link to verify, update billing, or “save” your account.
Defense: never click links in emails about your AI tool accounts. Open the tool the way you normally do, through your bookmark or your password manager, and check the account status there.
The thread running through all of it
The pattern across all six is the same. AI has lowered the cost of personalization, and personalization is what makes a scam land. Many of these manipulation techniques are already appearing across broader AI scam campaigns beyond freelancing environments.
The same shift is reshaping how enterprise security teams operate, with AI agents now triaging and investigating these patterns at scale. Most freelancers won’t have that kind of tooling.
The freelancer’s defense is slower, not faster. Slow down on anything that feels urgent. Verify through the channel you already trust. Don’t let a clean-sounding email or a friendly voice override the workflow that’s kept your business safe.
